I want to collect a series of mini howto and tips to help you make quick configurations and easy troubleshooting in Alfresco. I start by showing how to reset the alfresco admin password. In the Alfresco’s official wiki page you can find a useful documentation about security and authentication implementation, I will refer to it.
Note 1 – The following solutions are applicable for the embedded admin user according to the AlfrescoNtlm default authentication chain, so it is not considered any additional authentication subsystems like Active-Directory/LDAP instances or anyother external Single Sign-on systems.
Note 2 – In the default AlfrescoNtlm authentication mechanism the passwords are stored locally in the Alfresco SQL database as UTF16LE-encoded MD4 hashes (i.e. NTLM). Here’s the encoding steps for the string ‘admin’.
1. plain-text string ==> admin 2. UTF16LE-encoded string ==> a\x00d\x00m\x00i\x00n\x00 3. MD4 of UTF16LE-encoded string (NTLM) ==> 209c6174da490caeb422f3fa5a7ae634 (stored in the database)
SOLUTION 1. You know the credentials of at least one no-admin user (suppose “bob”).
Alfresco 3.2 and later
$ vi ALF_HOME/tomcat/shared/classes/alfresco-global.properties # Add this alfresco_user_store.adminusername=bob
Alfresco 3.0 and older versions
$ vi ALF_HOME/tomcat/webapps/alfresco/WEB-INF/classes/alfresco/authority-services-context.xml
<property name="adminUsers"> <set> <value>admin</value> <value>bob</value> </set> </property>
Restart Alfresco and login as this user. Now you have administrative privileges so update the admin user password then revert configuration.
SOLUTION 2. You do not know any user passwords but you have read/write access to the Alfresco DB schema.
mysql> use alfresco_db; SELECT anp1.node_id, anp1.qname_id, anp1.string_value FROM alf_node_properties anp1 INNER JOIN alf_qname aq1 ON aq1.id = anp1.qname_id INNER JOIN alf_node_properties anp2 ON anp2.node_id = anp1.node_id INNER JOIN alf_qname aq2 ON aq2.id = anp2.qname_id WHERE aq1.local_name = 'password' AND aq2.local_name = 'username' AND anp2.string_value = 'admin'; +---------+----------+----------------------------------+ | node_id | qname_id | string_value | +---------+----------+----------------------------------+ | 4 | 11 | 7A21990FCD3D759941E45C490F143D5F | +---------+----------+----------------------------------+ 1 row in set (0.00 sec)
In this example you can see the NTLM string value for ‘12345’ password. Run an update to the string_value column with node_id=4 and qname_id=11:
mysql> UPDATE alf_node_properties SET string_value='209c6174da490caeb422f3fa5a7ae634' WHERE node_id=4 and qname_id=10;
The new NTLM value is ‘209c6174da490caeb422f3fa5a7ae634’ (‘admin’ plaintext) so you can login to Alfresco using the default admin/admin credentials.
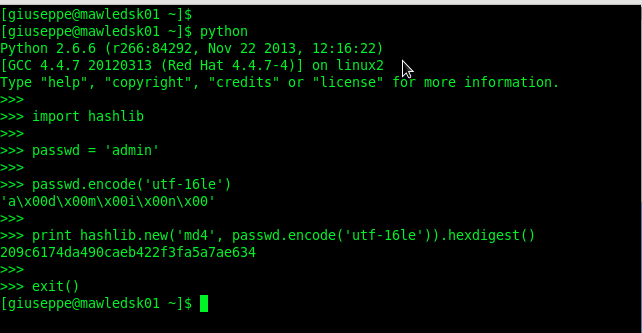
SOLUTION 3. Run a brute force attack on the Alfresco NTLM hash using MDCRACK (for test and studies only)
To complete this article I show a case study based on mdcrack bruteforce of the NTLM hash. This is intended to assist pentesters, system administrators and users in testing their own passwords, or other passwords for which they have been given permission to test, in order to determine the security of such passwords. I hereby disclaim any responsibility for illegal actions taken based on this post.
#NTLM for 'admin' : 209C6174DA490CAEB422F3FA5A7AE634 $ mdcrack -M NTLM1 -S 5 209c6174da490caeb422f3fa5a7ae634
 English
English Italian
Italian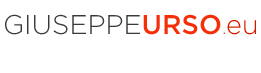


Solution number 2 worked for me; but only after restarting the alfresco instance
Nice tip! Relating to the note 2 gere’s my two cents. You can type in a linux console for generate “admin” password:
$ printf ‘%s’ “admin” | iconv -t utf16le | openssl md4
(stdin)= 209c6174da490caeb422f3fa5a7ae634
Thanks Cesar,
in this article I used the the python hashlib module to generate the md4 admin hash (see the image above). The GNU coreutils printf works well too.
Thank for tip
😉
Giuseppe